- Published on
Pearl CTF - Shadow Vault
- Authors

- Name
- 0x1622
We were given with a .apk file
I initially used apktool for decompling the application and view its contents.
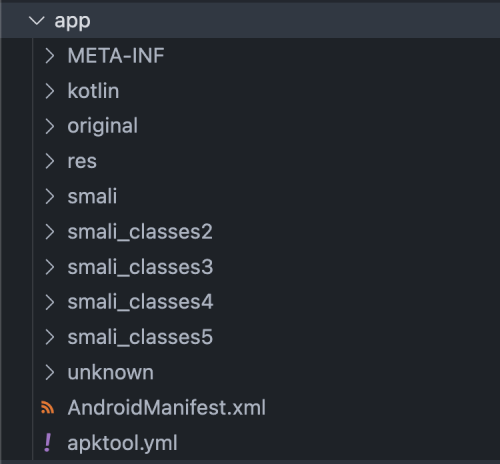
This was the basic structure of the contents inside the application. Nothing looks suspicious, and everything appears normal.
Next, I used Jadx-GUI for static analysis of the application while simultaneously starting Genymotion to observe its actual behavior.
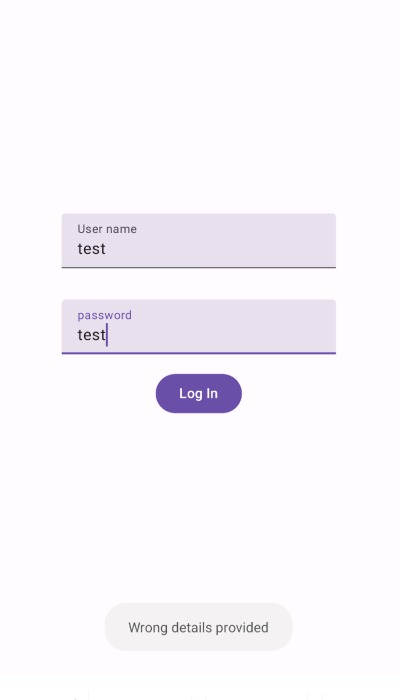
The application had nothing but just this login screen.
I then started looking for keywords like "User name" and "password" while statically analyzing.
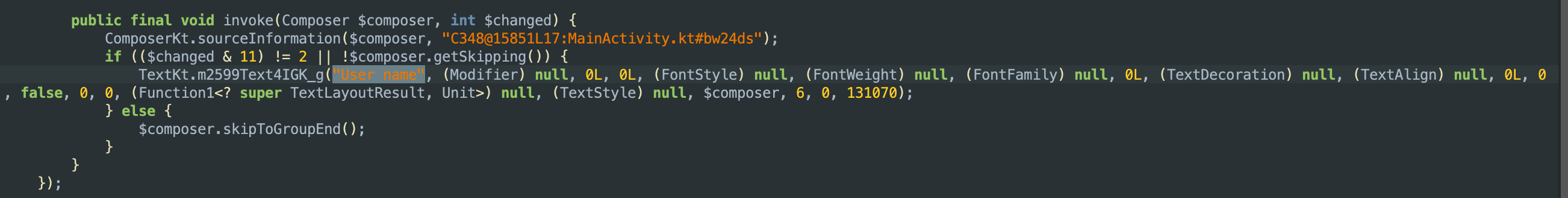
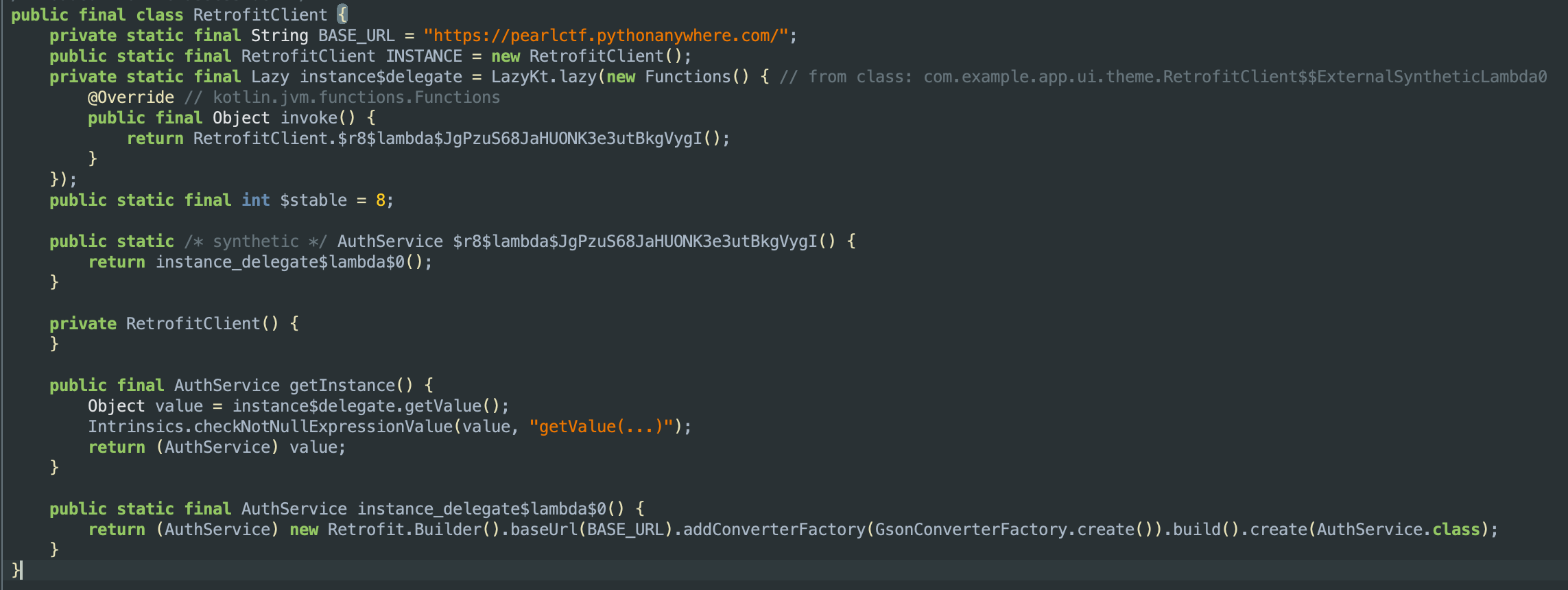
Here, you can see that the BASE_URL is set to the server-side of the organizing team. I made a ticket on Discord to ask whether the flag was on the server side or the client side, and they confirmed it was on the server side. At this point, all I needed to find were the endpoints of the BASE_URL.
The AuthService in the context of the provided code refers to an interface that defines the API endpoints for authentication-related operations.
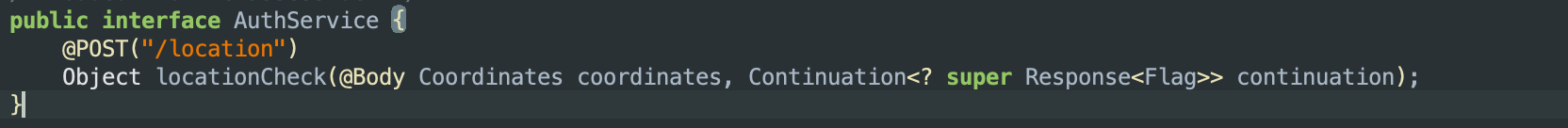
The AuthService was showing /location as its endpoint with a POST json request. I fired up Burp and sent a blank POST request to /location, which returned this response.
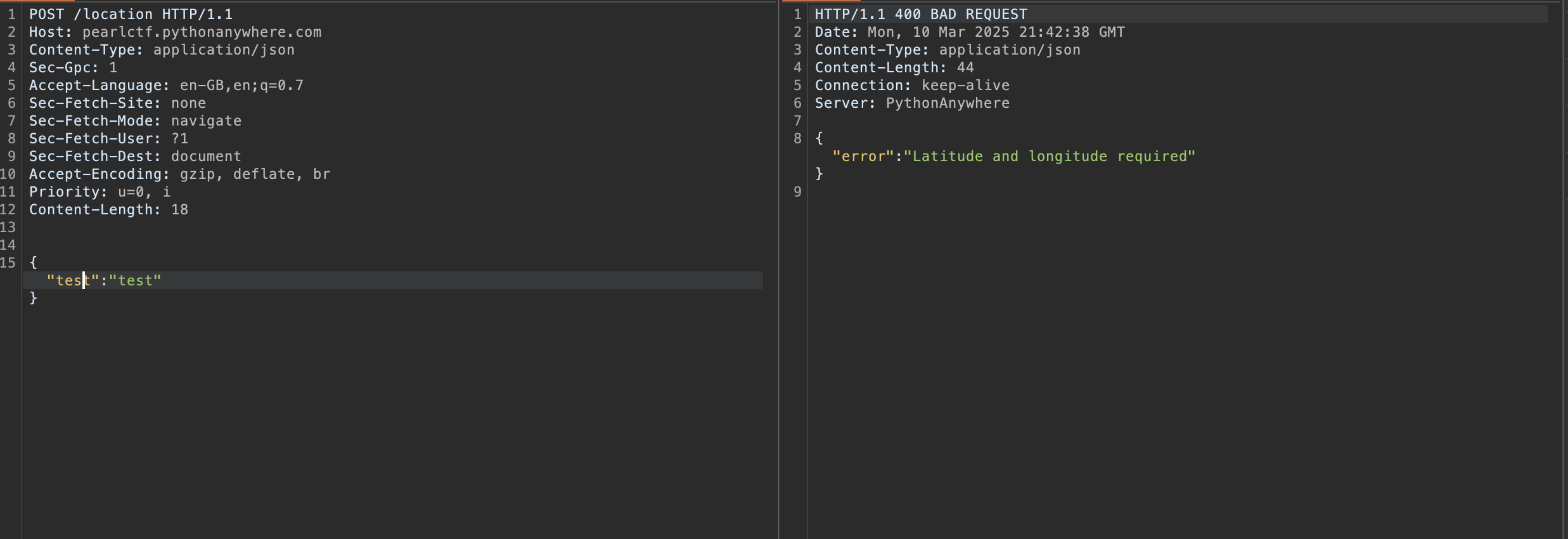
At this point, it was clear that:
- The request requires two parameters.
- We need to find the exact coordinates to get the flag.
I went back and searched for "Latitude" and "Longitude" (there were more than 50 results).
After some searching and analyzing, I finally located the relevant code.
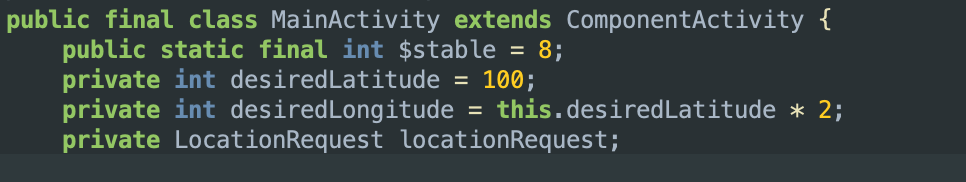
Here you can clearly see the value of Latitude being set to 100 while the value of Longitude as Latitude * 2
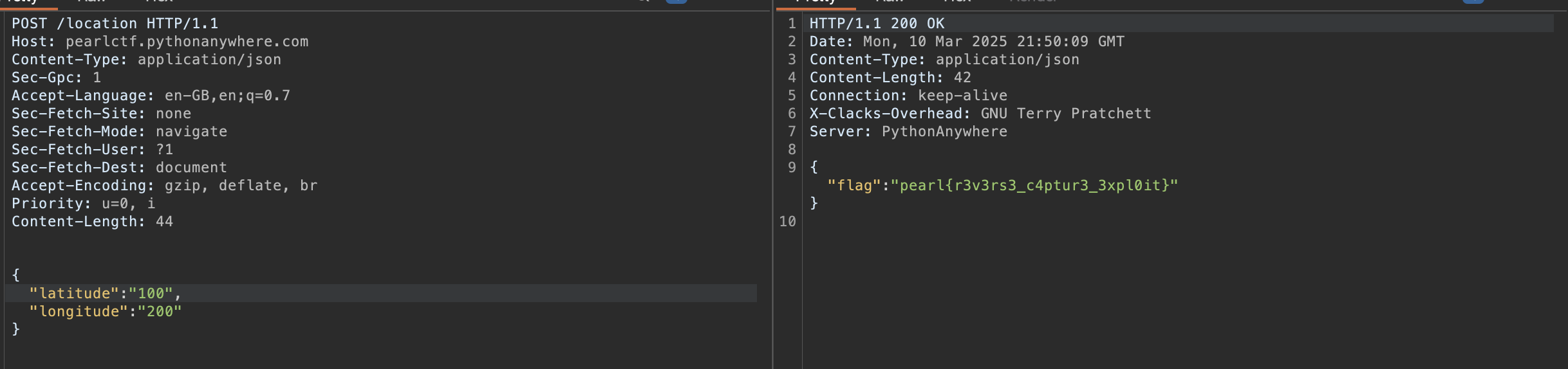
Thus i got the flag
pearl{r3v3rs3_c4ptur3_3xpl0it}
